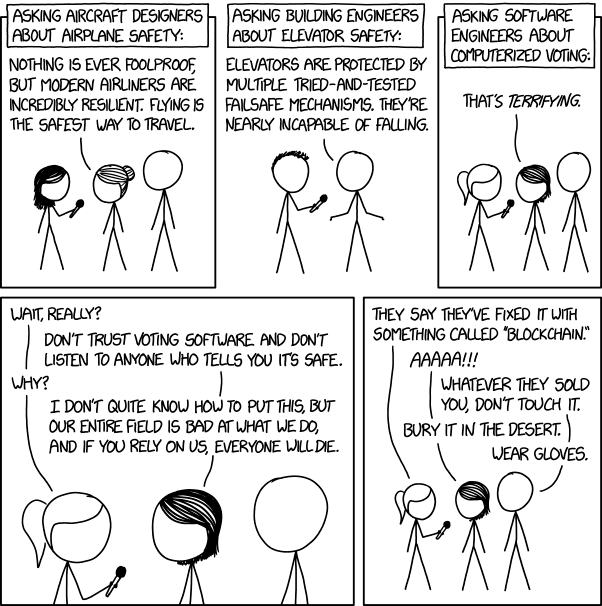
This xkcd comic basically sums up my recent life. WFI system? Never seems to be a problem. Bioreactors? Work like clockwork. Cell growth? We go that covered. The list goes on. And then we get to pure software systems, and I spend all my time and effort on them. I wish it was just my company, but lets be frank, this stuff is harder than it should be and don’t trust a single software company or consultant who wants to tell you otherwise.
I am both terrified and ecstatic as everything moves to the cloud. Terrified because these are the same people who can’t get stuff like time clocks right, ecstatic because maybe when we all have the exact same problem we will see some changes (misery loves company, this is why we all go to software conferences).
So, confessional moment done, let us turn to a few elements of a competent computer systems validation program (csv).
Remember your system is more than software and hardware
Any system is made up of Process, Technology, People and Organization. All four need to be evaluated, planned for, and tested every step of the way. Too many computer systems fall flat because they focus on technology and maybe a little process.
Utilize a risk based approach regarding the impact of a computer system impact on product quality, patient and consumer safety, or related data integrity.
Risk assessments allow for a detailed, analytical review of potential risks posed by a process or system. Not every computer system has the same expectations on its data. Health authorities recognize that, and accept a risk based approach. This is reflected across the various guidances and regulations, best practices (GAMP 5, for instance) and the ISOs (14971 is a great example).
Some of the benefits of taking this risk based approach include:
- Help to focus verification and validation efforts, which will allow you to better focus of resources on the higher-risk items
- Determine which aspects of the system and/or business process around the system, require risk mitigation controls to reduce risk related to patient safety, product quality, data integrity, or business risk
- Build a better understanding of systems and processes from a quality and risk-based perspective
Don’t short the user requirements
A good user requirement process is critical. User requirements should include, among other things:
- Technical Requirements: Should include things like capacity, performance, and hardware requirements.
- System Functions: Should include things like calculations, logical security, audit trails, use of electronic signature.
- Data: Should describe the data handling, definition of electronic records, required fields.
- Environment: Should describe the physical conditions that the system will be required to operate in.
- Interface: What and how will this system interface with other systems
- Constraints: discuss compatibility, maximum allowable periods for downtime, user skill levels.
- Lifecycle Requirements: Include mandatory design methods or special testing requirements.
Evaluate each of people, process, technology and organization.
This user requirement will be critical for performing a proper risk assessment. Said risk assessment is often iterative.
Build and test your system to mitigate risk
- Eliminating risk through process or system redesign
- Reduce risk by reducing the probability of a failure occurring (redundant design, more reliable solution)
- Reduce risk by increasing the in-process detectability of a failure
- Reduce risk by establishing downstream checks or error traps (e.g., fail-safe, or controlled fail state)
- Increased rigor of verification testing may reduce the likelihood by providing new information to allow for a better assessment
After performing verification and validation activities, return to your risk assessment.
Apply a lifecycle approach once live
- Apply proper change management
- Perform periodic reviews of the system. This should include: current range of functionality, access and training, process robustness (do the current operating procedures provide the desired outcome), incident and deviation review, change history (including upgrades), performance, reliability, security and a general review of the current verified/validated state.
- Ensure the risk assessment is returned to. On a periodic basis return to it and refresh based on new knowledge gained from the periodic review and other activities.
Do not separate any of this from your project management and development methodology
Too many times I’ve seen the hot new development lifecycle consider all this as an after thought to be done when the software is complete. That approach is expense, and oh so frustrating

13 thoughts on “Computer verification and validation – or what do I actually find myself worrying about every day”