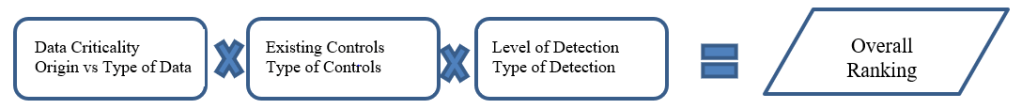
A quick overview. The risk-based approach will utilize three factors, data criticality, existing controls, and level of detection.
When assessing current controls, technical controls (properly implemented) are stronger than operational or organizational controls as they can eliminate the potential for data falsification or human error rather than simply reducing/detecting it.

For criticality, it helps to build a table based on what the data is used for. For example:

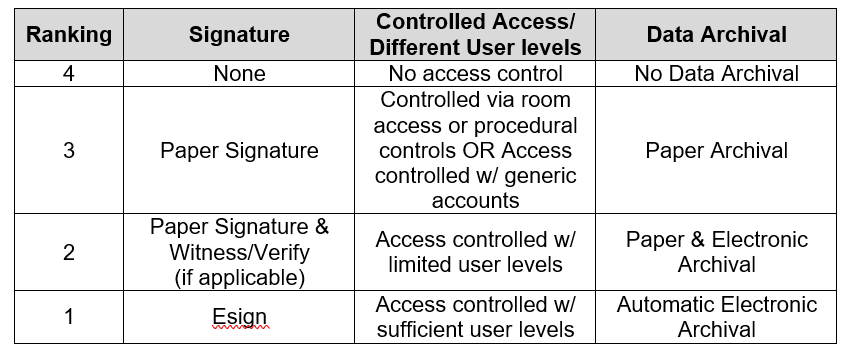
For controls, use a table like the one below. Rank each column and then multiply the numbers together to get a final control ranking. For example, if a process has Esign (1), no access control (3), and paper archival (2) then the control ranking would be 6 (1 x 3 x 2).
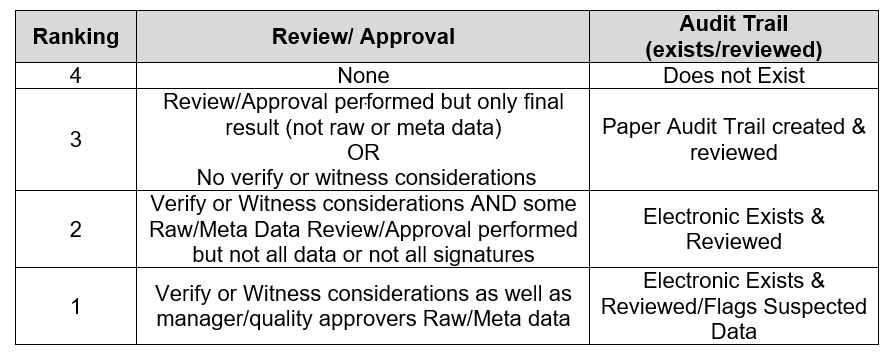
Determine detectibility on the table below, rank each column and then multiply the numbers together to get a final detectability ranking.
Another way to look at these scores:
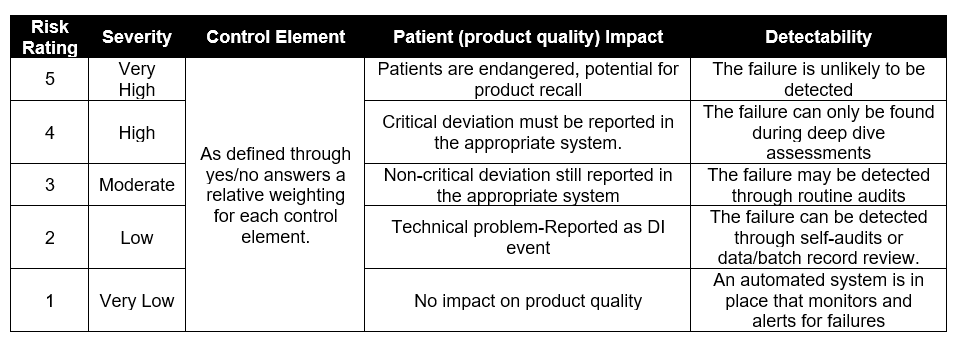
Multiple above to determine a risk ranking and move ahead with mitigations. Mitigations should be to drive risk as low as possible, though the following table can be used to help determine priority.
| Risk Rating | Action | Mitigation |
| >25 | High Risk-Potential Impact to Patient Safety or Product Quality | Mandatory |
| 12-25 | Moderate Risk-No Impact to Patient Safety or Product Quality but Potential Regulatory Risk | Recommended |
| <12 | Negligible DI Risk | Not Required |
In the case of long-term risk remediation actions, risk reducing short-term actions shall be implemented to reduce risk and provide an acceptable level of governance until the long-term remediation actions are completed.
Relevant site procedures (e.g., change control, validation policy) should outline the scope of additional testing through the change management process.
Reassessment of the system may be completed following the completion of remediation activities. The reassessment may be done at any time during the remediation process to document the impact of the remediation actions.
Once final remediation is complete, a reassessment of the equipment/system should be completed to demonstrate that the risk rating has been mitigated by the remediation actions taken. Think living risk assessment.

8 thoughts on “Risk Based Data Integrity Assessment”